Cyberattack Lifecycle and MDR Response: Detecting and Stopping Attacks at Every Stage


Cyberattacks rarely happen all at once. An attacker who compromises a network on Monday may not deploy ransomware until Thursday. Between initial access and the final payload, there are multiple stages where detection is possible and where containment can stop the attack before damage occurs. Understanding that sequence changes how you think about security monitoring.
This article maps the cyberattack lifecycle stage by stage, from reconnaissance through attack execution, and explains exactly what MDR detects at each phase and what response actions follow. For a broader look at how these detection scenarios translate into operational use cases, see our guide on common MDR use cases explained.
Understanding the Cyberattack Lifecycle

Why Cyberattacks Follow a Structured Process
Attackers follow structured processes because those processes work. Rushing from initial access to data exfiltration without establishing persistence, escalating privileges, and moving laterally increases the chance of detection and limits the attacker's reach. The structured approach allows attackers to operate more quietly, gather more access, and maximize damage or extortion power when they finally act.
For defenders, the structure is an advantage. Each stage produces observable signals. An attacker cannot move laterally without generating network events. They cannot escalate privileges without touching identity systems. They cannot exfiltrate data without moving it somewhere. Every stage of the attack lifecycle creates detection opportunities that MDR is built to act on.
Overview of the Cyber Kill Chain and MITRE ATT&CK Framework
The Cyber Kill Chain, developed by Lockheed Martin, describes seven stages of a cyberattack from reconnaissance to execution. The MITRE ATT&CK framework extends this model with a detailed catalog of specific attacker tactics, techniques, and procedures (TTPs) observed in real-world intrusions. MDR detection rules map directly to ATT&CK techniques, meaning each detection is tied to a documented attacker behavior rather than a generic alert condition.
MITRE ATT&CK is maintained continuously as new attack techniques are documented from incident data worldwide. MDR providers use it as the reference architecture for detection engineering, so as new techniques are added to the framework, detection coverage follows. This keeps MDR detection current against the actual methods attackers use rather than the methods that were common when static rules were written.
Why Early Detection Matters
According to the Mandiant M-Trends 2024 Report, the global median attacker dwell time was 10 days. Every day an attacker spends inside an environment undetected is another day of lateral movement, privilege escalation, and data staging. Detecting an attacker during reconnaissance or initial access produces a very different outcome than detecting them during data exfiltration. The earlier the detection, the fewer systems are compromised, the less data is at risk, and the faster containment completes.
Stages of the Cyberattack Lifecycle
Reconnaissance
Attackers Gather Information About the Target
Reconnaissance begins before any attack tool touches the target network. Attackers use open-source intelligence to map the organization's internet-facing infrastructure: exposed services, employee names and roles from LinkedIn, technology stack indicators from job postings, and domain registration data. This phase is largely passive and generates no alerts within the target environment.
Scanning Systems and Identifying Vulnerabilities
Active reconnaissance shifts to port scanning and vulnerability probing against internet-facing systems. Automated scanners test for open ports, service versions, and known vulnerability signatures. MDR network monitoring detects scanning activity through probe patterns, repeated connection attempts to multiple ports from the same source, and requests matching known vulnerability scanner signatures. While reconnaissance alone does not confirm an attack is imminent, documented scanning against specific vulnerabilities in the target's stack warrants investigation and accelerated patching prioritization.
Initial Access
Phishing Attacks
Phishing remains the most common initial access method across attack types. A user clicks a malicious link, opens an infected attachment, or enters credentials into a spoofed login page. The attacker gains either a malware foothold on the user's endpoint or valid credentials for an account in the environment. MDR endpoint monitoring detects the process execution that follows a successful phishing payload: a document spawning a PowerShell process, a script executing from a temporary directory, or a browser process making unexpected network connections.
Exploiting Vulnerabilities
Unpatched vulnerabilities in internet-facing systems give attackers a direct path into the network without requiring user interaction. Web application vulnerabilities, VPN appliance exploits, and remote code execution flaws in publicly exposed services are common entry points. According to the 2024 Verizon Data Breach Investigations Report, exploitation of vulnerabilities as an initial access vector grew 180% year over year, driven by attackers targeting VPN and edge device vulnerabilities specifically. MDR detection rules map to known exploit patterns and flag traffic matching exploitation attempts against monitored systems.
Credential Compromise
Stolen credentials obtained through phishing, credential stuffing, or purchase from criminal markets give attackers access that looks legitimate to authentication systems. The attack generates no exploit signature because it uses a valid username and password. MDR behavioral analytics identifies the deviation: an account authenticating from a new country, a login at an unusual time, or access to systems outside the account's established scope. The behavioral signal is the only detection available when credentials are the entry point.
Establishing Persistence
Malware Installation
After gaining initial access, attackers install persistence mechanisms to maintain their foothold if the initial access vector gets closed. Common persistence methods include scheduled tasks that execute malicious code at set intervals, Windows registry modifications that run malware on startup, and services installed under names that blend with legitimate system processes. MDR endpoint monitoring tracks all new scheduled task creation, registry modifications in startup keys, and service installations, flagging those that do not match known software deployment patterns.
Backdoors and Unauthorized Access
Backdoors give attackers a secondary access path that survives password resets, endpoint reimaging, and firewall rule changes. They may take the form of web shells installed on compromised servers, remote access tools configured to beacon out through allowed ports, or new local accounts created with administrative privileges. MDR process monitoring detects web shell activity through parent-child process relationships that indicate server-side code execution, and network monitoring flags persistent outbound connections on unusual schedules that match command-and-control beaconing patterns.
Privilege Escalation
Gaining Administrative Access
Most attack objectives require elevated privileges. Accessing domain controllers, modifying security policies, disabling backup systems, and deploying payloads across the network all require administrative access that a standard user account does not have. Attackers escalate privileges through exploitation of local vulnerabilities, abuse of misconfigured services, or pass-the-hash and token manipulation techniques that allow them to impersonate privileged accounts without knowing their passwords.
Abusing Misconfigured Permissions
Many privilege escalation paths do not require exploit code at all. Overly permissive service accounts, group policies that grant excessive rights, and misconfigured access control lists all provide legitimate escalation paths that attackers use without triggering vulnerability-based detection. MDR identity monitoring tracks privilege changes in real time: when an account gains administrative group membership, when a service account is granted new rights, or when a standard user account suddenly has access to systems it has never reached before.
Lateral Movement
Moving Across the Network
Lateral movement is where attackers expand from their initial foothold to the systems that hold their actual targets. They use legitimate administrative tools including Remote Desktop Protocol (RDP), Windows Management Instrumentation (WMI), and PsExec, specifically because these tools are present in most environments and their traffic blends with normal administrative activity. Detection requires behavioral baselines that distinguish legitimate administrative use from attacker abuse of the same tools.
Accessing Additional Systems
As lateral movement progresses, the attacker maps the internal network, identifies high-value targets, and moves toward them systematically. An account connecting to 30 internal servers over two hours using RDP is not administrative maintenance. It is reconnaissance and staging. MDR network monitoring detects these movement patterns through east-west traffic analysis, and endpoint monitoring tracks the sequence of systems each account reaches to build a picture of the attacker's path through the environment.
Data Exfiltration
Stealing Sensitive Information
Before executing the final attack objective, attackers stage and transfer sensitive data. In double extortion ransomware campaigns, exfiltrated data becomes the attacker's pressure point: pay the ransom to restore access, or the data gets published. In espionage campaigns, the data transfer is the objective. Exfiltration typically uses encrypted channels, cloud storage services, or legitimate file transfer tools to blend with normal traffic. MDR detects it through volume anomalies, destination analysis, and behavioral deviations from the account's established data movement patterns.
Preparing for Ransomware or Extortion
The period between exfiltration completion and ransomware deployment is often the last window where MDR can intervene before irreversible damage occurs. Attackers completing data staging begin disabling backups, deleting shadow copies, and positioning the ransomware payload for deployment. MCK's MDR threat detection specifically monitors for Volume Shadow Copy deletion commands, backup service termination, and security tool process kills that signal imminent ransomware deployment, triggering immediate containment actions at this stage.
Attack Execution
Ransomware Deployment
Ransomware deployment is the final stage and the one with the least recovery options once it completes. The payload encrypts files across all reachable systems simultaneously, starting from the most valuable data repositories and moving outward. MDR detection at this stage focuses on rapid file modification events, encryption process signatures, and ransom note creation. Endpoint isolation at the moment of confirmed execution limits the spread to systems already running the payload, preserving unaffected systems while the incident response process begins.
Data Destruction or Service Disruption
Not all attacks end in ransomware. State-sponsored threat actors and hacktivists sometimes pursue data destruction or operational disruption as their objective. These attacks delete or corrupt data rather than encrypt it, targeting backup infrastructure first to prevent recovery. MDR monitoring detects mass file deletion events, database truncation commands, and changes to critical system configurations that indicate destructive intent rather than ransomware staging. According to the IBM 2024 Cost of a Data Breach Report, destructive attacks produced the highest average breach costs across all attack categories, reflecting the difficulty of recovery when data cannot be decrypted or restored from backups.
How MDR Detects and Responds at Each Stage
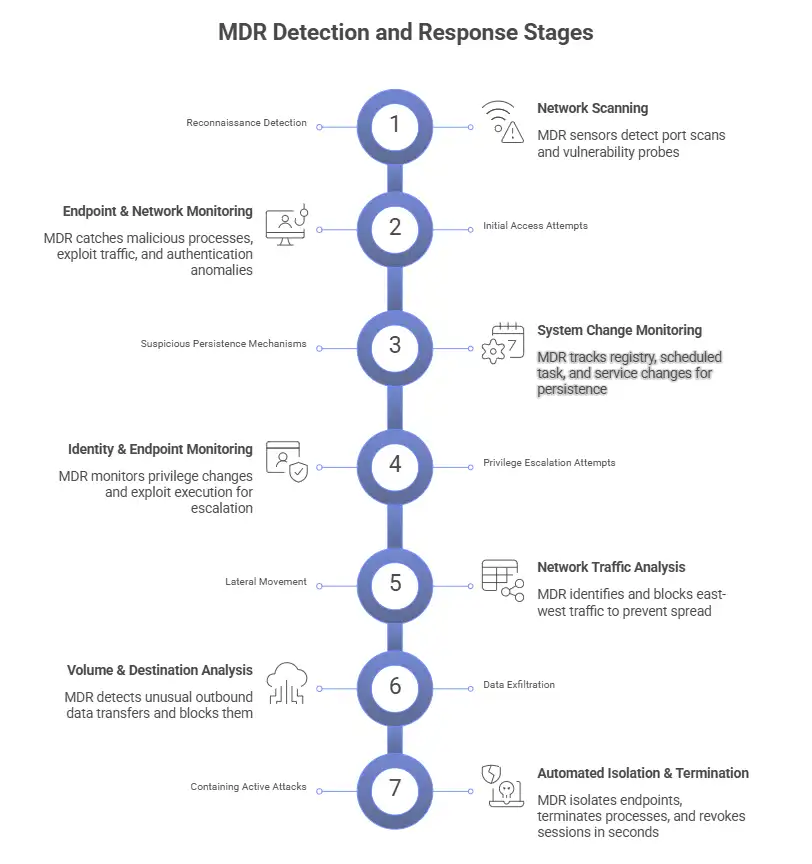
Detecting Reconnaissance Activity
Reconnaissance detection in MDR focuses on active scanning rather than passive OSINT collection, which leaves no trace in monitored systems. Network sensors detect port scan patterns, service enumeration traffic, and repeated probe attempts against specific vulnerabilities. When scanning activity specifically targets services with known unpatched vulnerabilities in the monitored environment, MDR escalates the observation to the client as a high-priority patching recommendation, treating it as attack preparation rather than routine internet noise.
Stopping Initial Access Attempts
MDR detection at the initial access stage operates across three vectors simultaneously. Endpoint monitoring catches malicious process execution that follows phishing payload delivery. Network monitoring identifies exploit traffic against internet-facing services. Identity monitoring flags authentication anomalies that indicate credential misuse. Catching initial access before persistence is established produces the cleanest containment outcome: one compromised endpoint or one account to address, rather than an attacker who has had days to entrench across the environment.
Identifying Suspicious Persistence Mechanisms
Persistence detection requires monitoring every system change that survives a reboot. MDR endpoint monitoring covers scheduled task creation, registry startup key modifications, new service installations, and account changes in real time. Each new persistence mechanism gets evaluated against a baseline of known software deployments in the environment. A scheduled task created by a known patch management tool scores low. A scheduled task created by a process that spawned from a Word document scores high and triggers immediate investigation.
Detecting Privilege Escalation Attempts
MDR identity monitoring tracks every privilege change in the environment: group membership modifications, role assignments, service account permission changes, and local administrator additions. Escalation attempts through known local privilege escalation vulnerabilities generate endpoint detection signals from the exploit execution. Escalation through misconfigured permissions generates identity monitoring signals when a standard account suddenly operates with administrative scope. Both paths are covered under a unified MDR monitoring operation rather than requiring separate tools for each detection type.
Blocking Lateral Movement
Lateral movement is the stage where MDR intervention produces the most direct attack containment. Blocking an attacker at this stage prevents them from reaching domain controllers, backup infrastructure, and the high-value data repositories that are their actual targets. MDR network monitoring identifies movement patterns through east-west traffic analysis. When lateral movement is confirmed, analysts revoke the credentials being abused, block the administrative protocols being used, and segment the network portion the attacker has reached. The attacker loses their access paths without the malicious process reaching critical systems.
Preventing Data Exfiltration
Data exfiltration detection uses outbound volume baselines, destination reputation analysis, and behavioral deviation scoring for each account. When an account begins transferring data volumes that exceed its established normal by a significant margin, or when transfers go to external destinations the account has never used, MDR generates a high-priority alert and analysts begin blocking the transfer and preserving forensic evidence. Stopping exfiltration before it completes removes the double extortion pressure from ransomware operators and limits the regulatory exposure from data breach notification requirements.
Containing Active Attacks
When an attack reaches execution stage, MDR response shifts from investigation to immediate containment. Affected endpoints get isolated from the network within seconds of confirmed malicious activity. Malicious processes get terminated. Active sessions using compromised credentials get revoked. The response actions execute in parallel across all affected systems rather than sequentially, limiting the spread to systems already running the payload. According to the Ponemon Institute 2024 research, organizations with automated containment capabilities reduced average breach costs by over $1.7 million compared to those using manual-only response processes.
How MDR Technology Covers the Full Attack Lifecycle
No single tool provides detection coverage across all seven stages of the attack lifecycle. Reconnaissance and lateral movement require network-layer visibility. Persistence and privilege escalation require endpoint-level process monitoring. Credential attacks require identity behavioral analytics. Data exfiltration requires outbound traffic analysis combined with user behavior baselines.
MDR integrates these data sources under a single detection and response operation. Endpoint Detection and Response (EDR) covers host-level process activity and file system changes. Network Detection and Response (NDR) covers traffic patterns between systems and outbound connections. SIEM aggregates and correlates log data across all sources. Threat intelligence ties observed behaviors to known attacker techniques from the MITRE ATT&CK catalog. The detection rules that sit across these layers are what translate raw telemetry into the stage-specific alerts described above.
Closing Thoughts
Every cyberattack gives defenders multiple detection opportunities before damage occurs. Reconnaissance, initial access, persistence, privilege escalation, lateral movement, and data exfiltration all produce observable signals. The question is not whether those signals exist. The question is whether your security operation is watching for them and has the response capability to act when they appear.
MDR covers the full attack lifecycle by combining continuous behavioral monitoring, MITRE ATT&CK-aligned detection rules, and 24/7 analyst coverage into a single operation. MCK delivers MDR for SMEs across the USA, Canada, and UK, with detection coverage mapped to every stage of the attack lifecycle from the first day of deployment. Contact MCK to discuss how lifecycle-aware MDR protection fits your environment.
The next article in this series covers future trends in MDR technology and where managed detection and response is heading as AI, automation, and threat intelligence continue to advance.
